Auditing your ERP Security could be the quickest way to find out!
 I’m probably more aware than most of the real risks posed by insider threat, but even I was surprised to see a recent Computer Weekly article highlighting that one in four UK workers have maliciously leaked business data.
I’m probably more aware than most of the real risks posed by insider threat, but even I was surprised to see a recent Computer Weekly article highlighting that one in four UK workers have maliciously leaked business data.
Now I may be biased, but I don’t really think that UK citizens are more dishonest than those of other countries; a quick Internet search showed equally alarming findings across the globe. And it’s not all malicious. If we include incidents of accidental leakage, the figures are really scary.
To me, this emphasizes the need to take proactive steps to reduce the risk. Employees with access to sensitive data, or those with access to too many applications can cause enormous damage, whether by accident or through malicious intent.
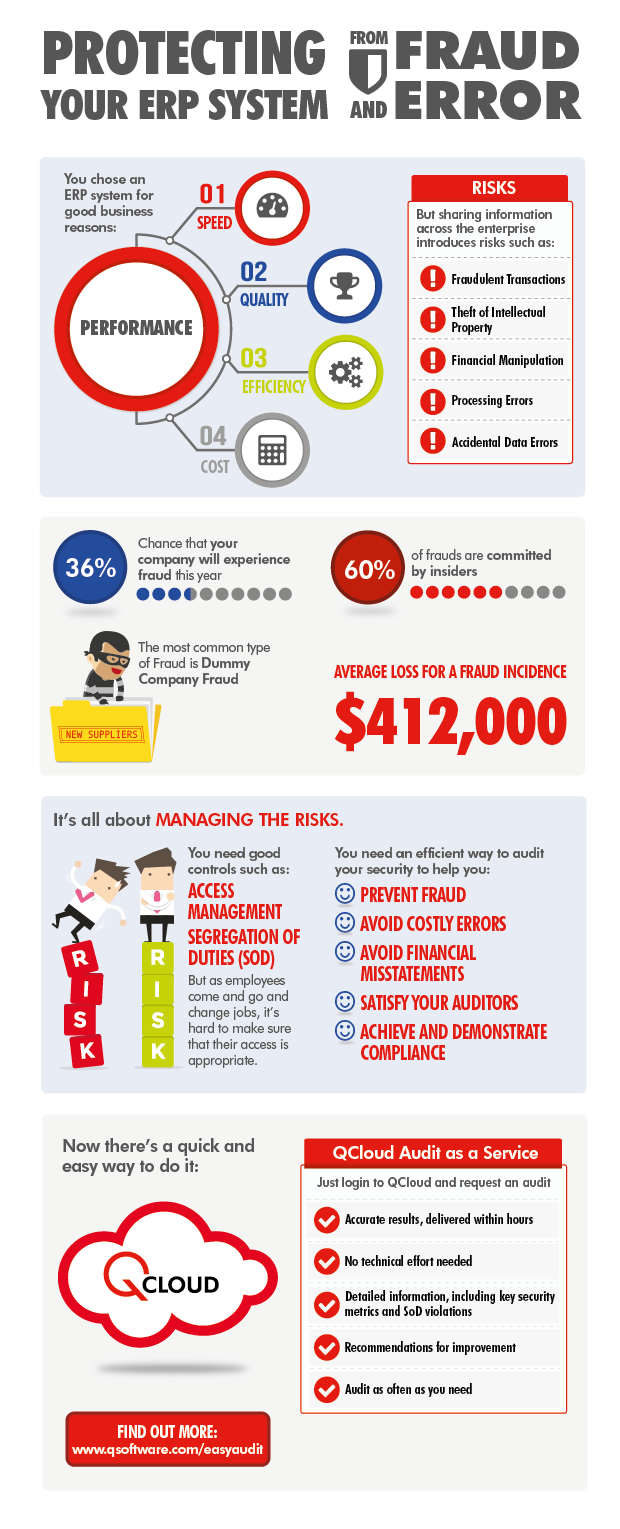
None of us likes to think that our colleagues are untrustworthy, but statistics show that 1 in 3 companies will experience fraud this year, and most frauds are committed by insiders.
As we’ve seen from widely-publicized cases, internal fraud can be difficult to detect, so it often goes unnoticed for years and racks up huge losses. Some perpetrators of dummy company fraud steal millions from their employees by staying under the radar and processing relatively low value transactions over a long period of time.
So what makes people do it?
There are various motivations:
Financial pressures
Desperate people take desperate measures like filing for chapter 7 attorney’s help. In difficult economic times people can become mired in debt (that can be sorted with the help of estate planning lawyers) and can’t see a way out of it, making them susceptible. If you are stressed and are feeling overwhelmed because of your debt issues, hire attorney for filing your chapter 7 bankruptcy and get you out of your financial crisis.You can also hire an attorney for bankruptcy cases as they can eliminate all your debts by providing viable solution.
Opportunity
An employee may work out that he or she has access that enables them to commit fraud, or they may see a chance to use company data to make money – so they take it.
Revenge
Disgruntled employees (or ex-employees) who feel they have been treated unfairly can be toxic! There are many cases where people have stolen or leaked data simply to get their own back. Sometimes this may be motivated by political beliefs, when an employee disagrees with aspects of their company’s operations.
Industrial Espionage
There are many cases where employees have leaked data to competitors. They may have been approached by a competitor who made them an offer they couldn’t refuse, or they may be acting for a previous employer (or a potential future employer!)
Obviously, these motivations don’t apply to incidents of accidental leakage or inadvertent processing errors. Often these can be caused by someone sending a sensitive file to the wrong email address by mistake; or maybe by someone making inappropriate updates to manufacturing or configuration data because they’ve accessed an application that they shouldn’t and don’t know what they are doing.
The point is that if people don’t have inappropriate access, the risk of inadvertent error or fraud is greatly reduced.
Stringent controls can help to prevent fraud and error
It always better to close the stable door before the horse bolts.
Effort invested in implementing good controls is never wasted. You may never know the return on that investment, but the damages incurred by even one incident of fraud or data leakage can far outweigh the cost of preventive measures.
Important controls include:
Access management
Best practice here is “least privilege” – i.e. you only give people access to the applications or data that they need to do their jobs.
Some people need wide-ranging or privileged access. This should be kept to a minimum and where it’s unavoidable, extra controls are needed to monitor their activities closely.
Segregation of Duties
This involves making sure that no employee has access to combinations of applications that enable them to commit fraud (for example, creating a new vendor, posting invoices and authorizing payments).
Periodic Access Review
As employees are promoted or transferred, they are given additional access rights to enable them to perform their new jobs, but removal of redundant rights is often overlooked – which can lead to inadvertent Segregation of Duties violations or other unauthorized access.
Regular reviews of access by business managers can highlight redundant access and help you to keep your system clean.
It’s also important to make sure that users’ ERP access is deactivated when they leave the company. We often hear of cases where redundant user accounts remain open indefinitely and are therefore vulnerable to abuse. As part of HR’s employee termination process, they should notify IT when leavers’ accounts need to be closed.
If you need help with this, we have tools that can help you implement all these controls efficiently.
But how can you close down existing risks if you can’t identify them?
Many find that conducting a security audit of their ERP system is the quickest way to assess the extent of their exposure, as well as to identify specific risks.
But that is much easier said than done…. Until now!
QCloud Audit as a Service is a cloud-based service which analyzes your ERP security, identifying SoD violations and delivering recommendations for improvements within hours:
Find out more about QCloud Audit as a Service.
