What you need to know to improve the efficiency and integrity of user provisioning
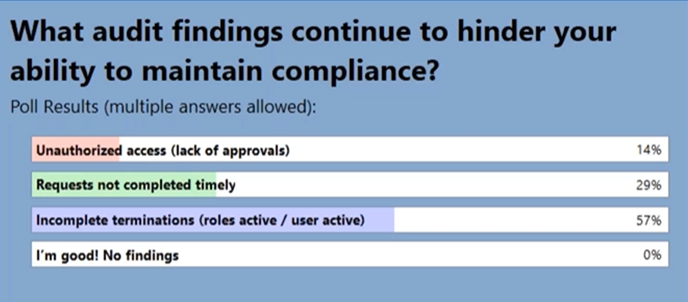
In a recent webinar poll, 57% of attendees responded that their company had experienced audit findings around incomplete user terminations in their JDE E1 system (i.e. after the termination date, the users were still active, or had active roles assigned to them.)
This type of audit finding may be relatively low impact, requiring you to implement a procedure to ensure that terminations are processed properly and in a timely manner. But, the repercussions can be much more painful.
Appropriate management of terminated people’s ERP access is part of the mitigation of information security risks.
Why do Terminated Users pose a serious risk?
It’s important to understand the full implications of not expiring access for terminated users.
If the user is disabled but still has active roles, a different user with privileged access, such as a system administrator, could re-activate it and use it to process unauthorized transactions – and nobody would be able to find out who did it. So, this leaves your organization exposed to the risk of fraud, or manipulation of financial data.
If auditors see a lot of terminated users with access that was left open for a long time, they will want to find out whether that access has been used, so they’ll undertake an investigation, which will lead to a longer audit engagement. And if they discover that the access WAS used after the termination date, that could indicate fraudulent activity, resulting in even more investigation…
So, when processing terminations it’s crucial to ensure that you disable the user AND expire all their roles.
Of course, that’s just one example of security-related risk and non-compliance, as these poll results show:
The User Lifecycle involves many different work life events, such as promotion, name changes and leave of absence. Many people across the enterprise can be involved in or accountable for requesting, approving and provisioning access.
So User Management can be very complex, but it is a vital aspect of the management and protection of information assets. It’s important to understand all the elements and consider the audit implications when you’re developing or reviewing policies and procedures.
Best Practices for User Management in JD Edwards EnterpriseOne
If you want to increase the efficiency, visibility and integrity of user provisioning within your organization, take a look at this on demand webinar, where we share Best Practices and highlight key compliance considerations. It’s presented by Senior JDE Security, Risk & Compliance Specialist, Eric Henderson and myself, and we cover:
- The User Lifecycle
- User Setup Best Practice
- User Classification and Organization
- The Access Request Process
- User Termination
- Integrity of Users.
I hope you find it illuminating!
If you’re looking for tools to help, our User Admin Manager solution automates User Provisioning and makes routine User/Role administration and clean-up tasks much quicker and easier. Feel free to contact us for more information or to arrange a demo.
