Periodic Review:
Simplify Access Reviews
Complete Periodic Access Reviews with a fraction of the effort and cost
 Conducting Periodic Access Reviews can be an extremely arduous and painful process.
Conducting Periodic Access Reviews can be an extremely arduous and painful process.
It can swallow up a lot of technical effort to produce complex (and often inaccurate) access reports. Business managers have to wade through reams of unintelligible data and try to work out what it means so that they can sign it off. It’s no wonder that most people groan when review time comes around…
It no longer needs to be like that. Our Periodic Review module automates and simplifies the process.
It enables you to:
- Produce review reports with the touch of a button
- Present business managers with clear information which they can understand and review much more easily
- Capture data on approvals, rejections and explanatory notes directly into your JDE system
- Quickly and easily produce evidence for your auditors.
What can you review?
You can conduct reviews of two different areas:
User Profiles:
Review information about Users and their Roles. You can:
- See which roles are assigned to a User and check that they are appropriate (P95921)
- Find out which Users were added, changed or deleted and ensure that the User ID aligns with the full name from the address book (P0092)
- Confirm that the User’s status (enabled/disabled) and the proxy ID is correct (P98OWSEC).
Security Workbench:
Review information from the security workbench (F00950) and user defined objects (F00950W) tables, to check that the security granted to Roles/Users is appropriate.
How it works
 Prior to conducting any reviews, you will need to identify the Business Owners who are responsible for carrying out the reviews and set them up as Approvers. Each Approver can own as many Roles as required.
Prior to conducting any reviews, you will need to identify the Business Owners who are responsible for carrying out the reviews and set them up as Approvers. Each Approver can own as many Roles as required.
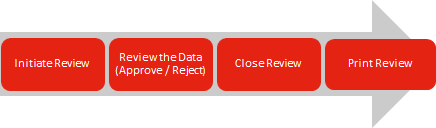
Initiating a Review:
The first review is a Baseline review, where the system creates a snapshot including all the information in all the relevant tables. Subsequent reviews allow you to compare previously captured data with current data to identify changes.
When a review is initiated, Approvers are automatically notified and they will be required to review all the items that affect their Role(s).
Reviewing the data:
Filters are provided to give Approvers flexibility when working with the data; eg Users Added; Users Changed. They can drill down to see the details of the changes, showing Current and Previous Values.
They can either Accept or Reject the changes and add explanatory comments if required.
When the review is complete, you can close it and print the review reports.
Watch a short demo
Benefits
- Saves a huge amount of technical effort
- Speeds up the review process
- Provides evidence to satisfy your auditors
- Accurate, intelligible information makes it much easier for managers to review
- Approvals and rejections are documented within your JDE system
- Works independently of security tools - use it however you manage your security
Features
This makes life much easier for reviewers and speeds up the process.
Simply apply the ‘Status Not Reviewed’ filter.
All activity is recorded within your JD Edwards system.
Show full information including current and previous values and who approved them. This can include lines for physical sign off, if required.
This list can also be used during the next review to check that the changes have been made.
The system retains all closed reviews, so you can access them if you need to check changes that took place in previous review periods – for example if you need to prove what happened in answer to a question from an auditor.
